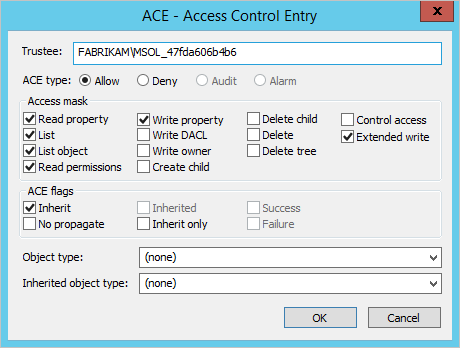
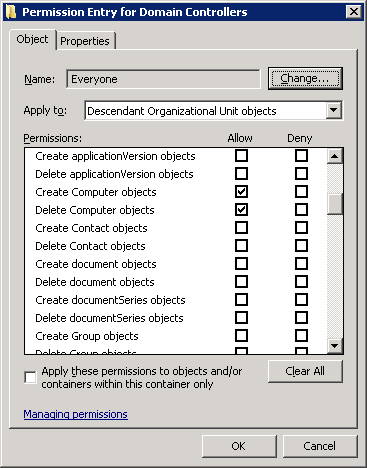
Active Directory and BitLocker – Part 2: Schema update, ACE settings, Password Recovery Viewer – 4sysops

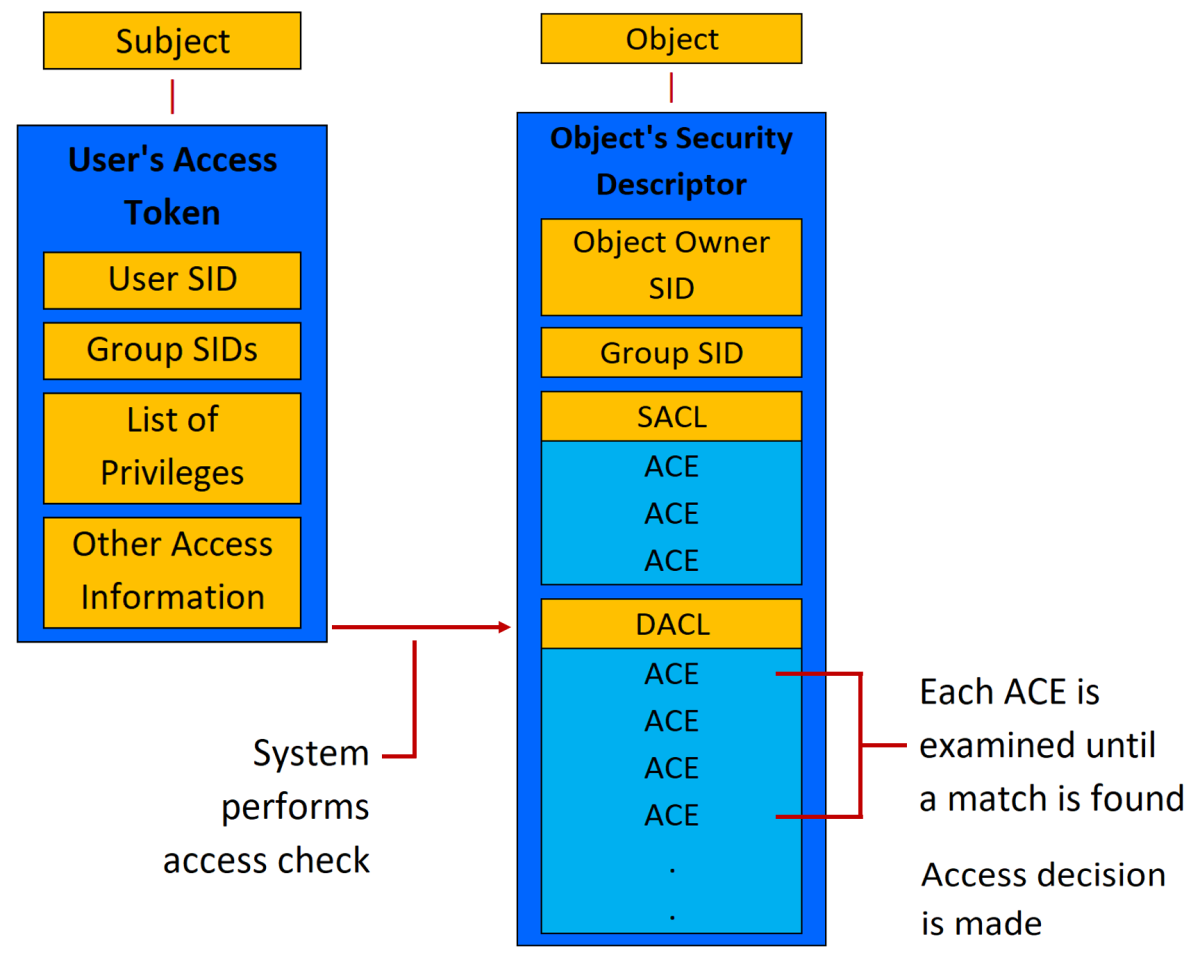
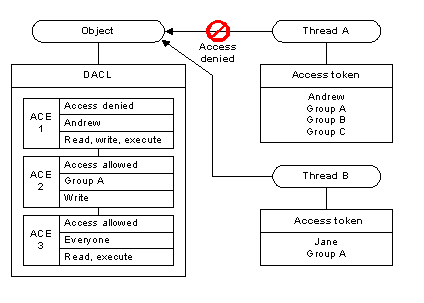
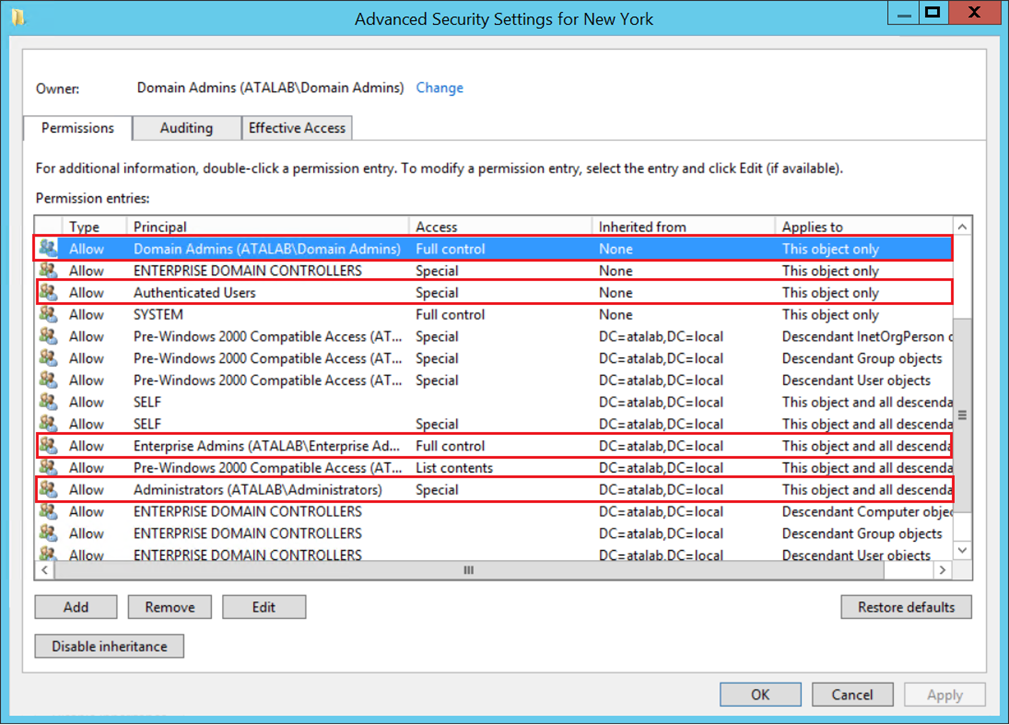
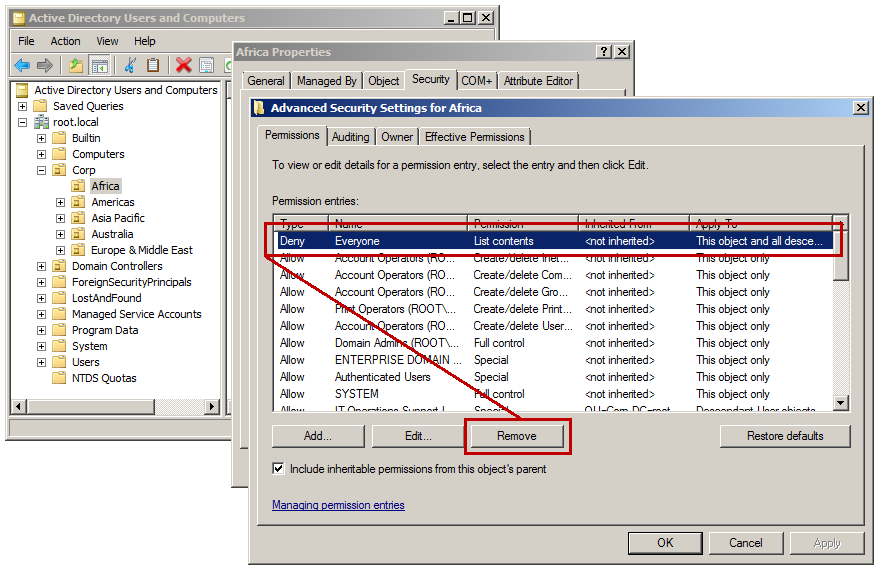
Active Directory Security Blog: Active Directory Access Control Lists (ACLs) - "Actual" Attack and Defense
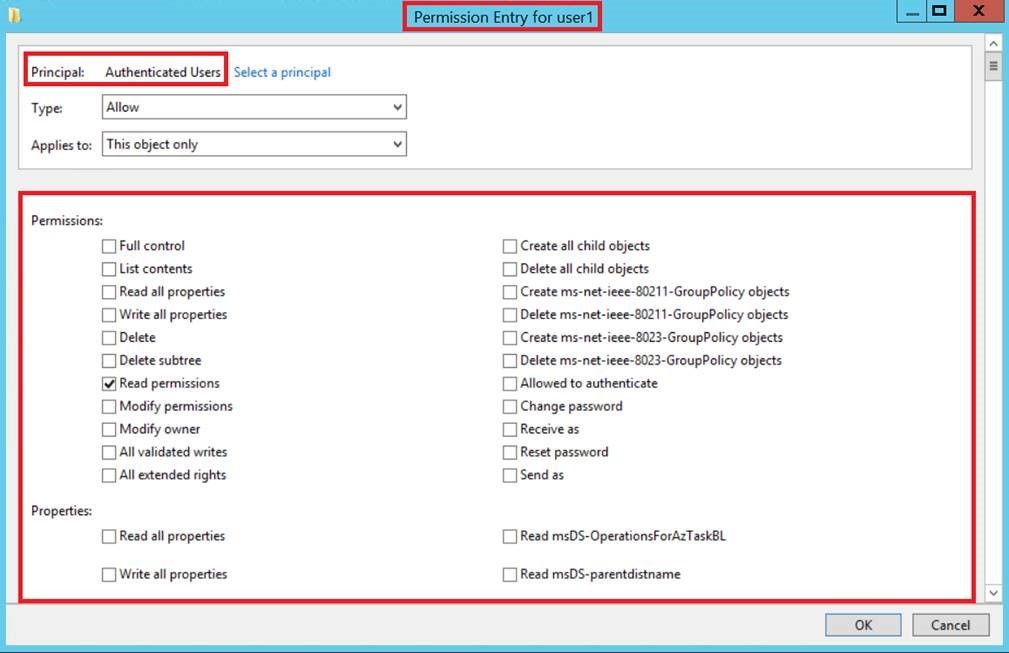
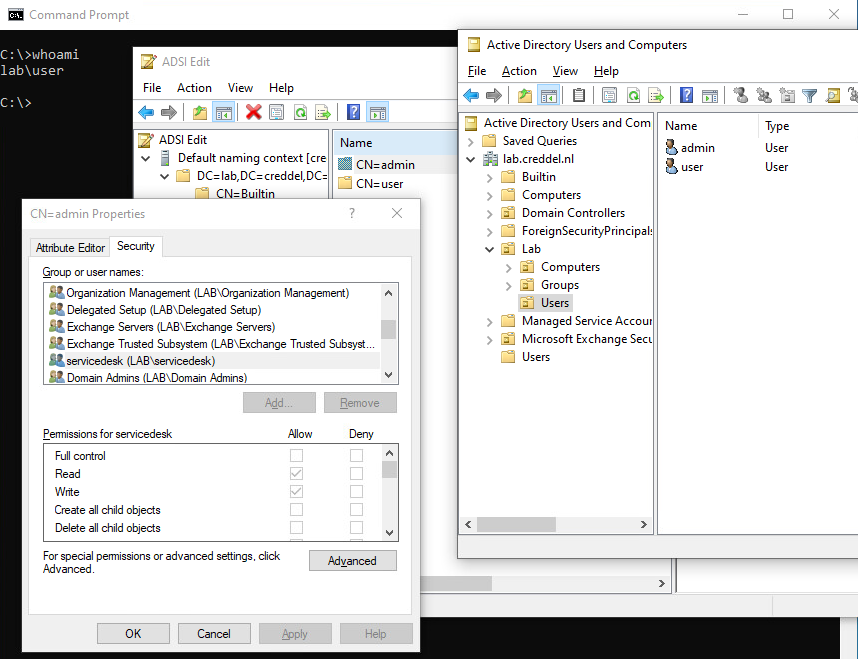
Active Directory Security Blog: How To Easily Identify & Thwart Sneaky Persistence in Active Directory